There’s a new trick up the Internet bad guy’s sleeves and it’s a doozy. Instead of installing keyloggers or other capturing tools they install a proxy server and set your browsers and other web apps to use it. A proxy server is a tool that re-directs web traffic to the proxy which then forwards it on to the site you asked for. For example, when I open google.com at work my browser asks the office proxy server for the page which checks against a list of allowed sites and then sends my computer google.com (assuming its allowed and safe). It’s a man in the middle. Advanced programming techniques have allowed nefarious characters to package an entire proxy server into a small easily executed file.
Once the proxy has been enabled on your system all of your traffic gets directed to it, which then forwards to the dark web servers so the bad guys can see the bank site and password you typed in. Here’s the rub, you don’t usually know this is happeing. Their system is a true proxy and is returning the pages you’re asking for. You might notice a delay or you may get errors when you try to go to certain sites that say “Proxy Error”. The other problem is that this type of software is a legitmate tool so most Anti-Virus or Anti-Malware software doesn’t detect or flag it.
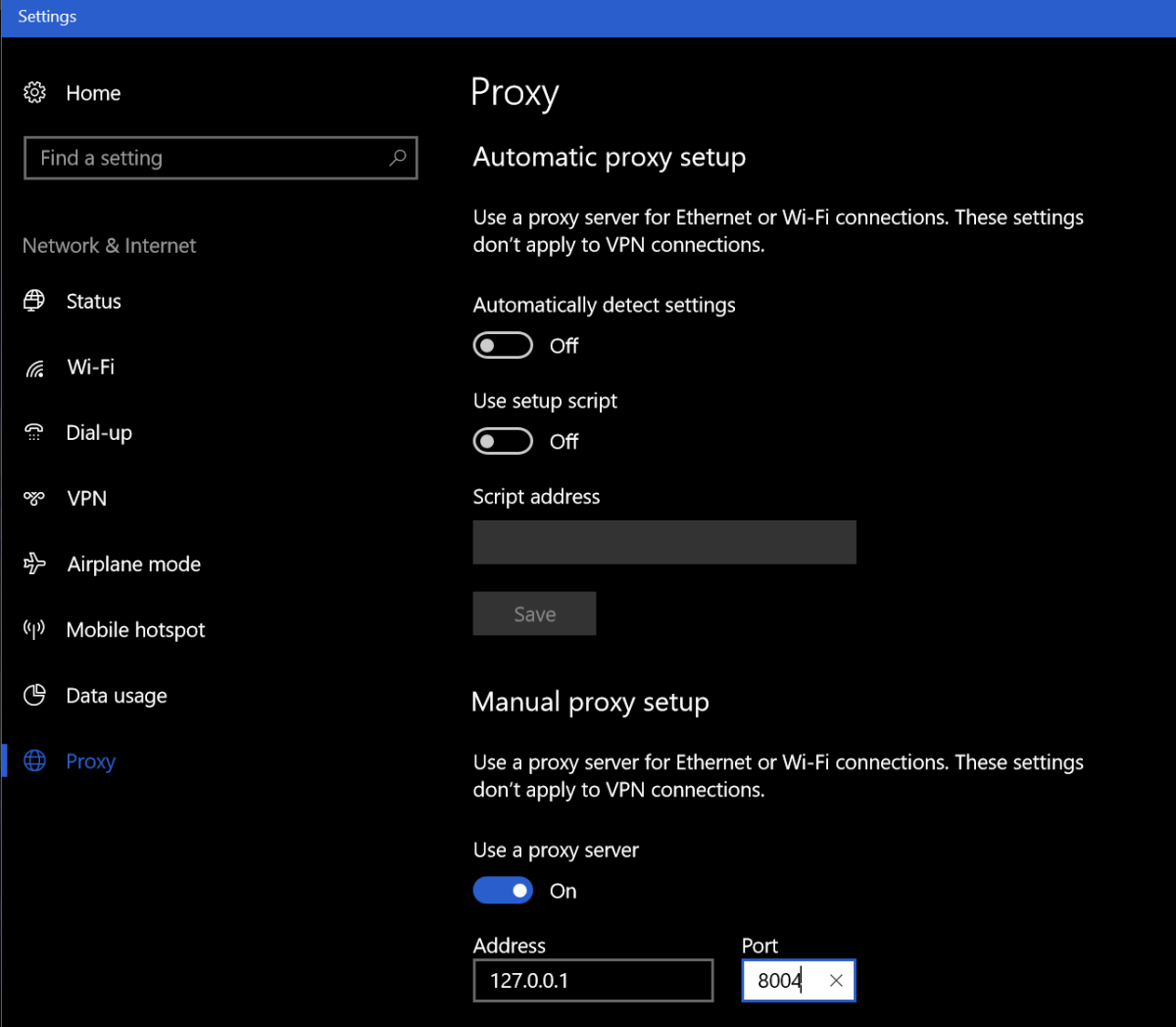
How do you know if you’ve been hit by this type of malware? Besides the afore mentioned “Proxy Error” you may notice unusual delays in your browser or web apps. The first thing to check is your Browser’s proxy settings. These are different for every broswer and every Operating System so Google “My browser proxy settings” and “My Windows Version” to see where to look on your system. When you get there, you should not see an address of 127.0.0.1, if you do this is an indication you’re a victim of a proxy attack. You’ll know for sure if you turn the proxy setting off, reboot, and find it turned back on (assuming your not on a mananged PC where you IT staff is doing this).
You can also go to a site like http://www.ipchicken.com and see if the public IP address it shows you matches the one on your internet modem / gateway’s admin page. If it doesn’t this is proof your web traffic is being re-routed through a foreign IP.
You’re being proxied, now what? Follow the instructions below at your own risk, I’m not in-front of your computer and each situation is unique. This is general advice and you are responsible for your actions, not me or whatdouknow.com. If you have a backup available you should consider formatting your hard drive and re-installing everything.
I’m going to assume your operating system is Windows. I’ve not seen this type of attack on Linux or MACs yet. So, first open PowerShell (search for it or find it in the start menu). Once you have it open type: Netstat -n -o and press enter. This is going to show you all the open network connections on your computer and the PIDs (Process ID) for the software that opened them. We’re looking for a line or lines that match what you saw in the browser settings of your computer.

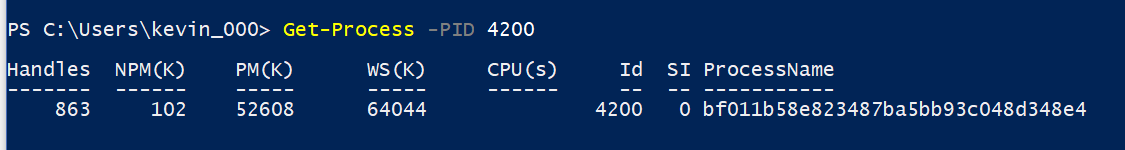
Once you’ve found it open another PowerShell session. Type: Get-Process -PID Number where number is the PID number that corresponds to the PID of your Netstat command (4200 in my case). Press enter and PowerShell will show you the name of the process. Write this down or type it into Word or notepad.
Now open task mananger (CTRL+ALT+Delete, click TaskManager) and find that process in the list of running apps. Right click on it and choose Open File Location, this will launch Windows Explorer and go to the directory that contains this file. Go back to the task manager and right click on the file again, this time choose End Task. Now go to the Explorer window you just opened and delete the entire folder. Just ending the task won’t stop the software from running again the next time your reboot your computer but you can’t delete the file until you’ve ended the task so the order is important here.
Once you’ve killed the task and deleted the file run Netstat -n -o again you should no longer see connections from 127.0.0.1. If you do, you may have more than one copy of the proxy attack installed, keep repeating the process until you’ve gotten them all. Always right down the name of the process. After you’ve stopped them all and deleted all their files we’ll need to clean up the registry.
Type Regedit in the search or run bar to open it. Right click on computer (top left) and choose find and search for the IP and Port numbers you found in your Netscan. If you find a match, delete the value by right clicking on the entry and choosing Modify, then clear the Value box and click OK. Press F3 to keep searching. Repeat the process until you see the “Finished Searching through the Registry” message pop-up. If you found more than one proxy on your system repeat the process until you’ve cleared all of them.
Now we’ll search the registy for the software entries. Right click on computer (in Regedit) and click find. Then enter the name of the process you found when you ran Get-Process in PowerShell. This time instead of deleting the value we’re going to delete the Key (folder) or Record itself. Right click on whatever it is and choose delete, click yes when prompted. Press F3 and keep searching / deleting until you get to the end of the registry. Repeat this process for every copy that you found.
Now go to your Proxy settings and turn it off. Then reboot your computer. When it comes back up everthing should be back to normal. Run the Netstat -n -o command again in PowerShell to be sure you got everything cleaned up. Go change all of your passwords for everything.

Thank you! This was very useful!
LikeLike