It has been interesting to watch backup technology evolve over the years. Technological innovations like volume snapshots have made restoring from a backup one of the primary means of recovering from IT issues quickly. It hasn’t always been that way though. In the not-so-distant past, many businesses didn’t value having backup copies of digital information. They operated in a hybrid world where paper was still a functional fallback.
Somewhere between the mid to late nineties paper fell out of being an operational option almost entirely. More data existed only in a digital form. There wasn’t a “hardcopy” someone could retrieve from a filing cabinet. Most business leaders and workers hadn’t really seemed to notice the transition from hybrid to fully digital. On May 5th, 2000, a young Filipino computer science student brought the revelation to everyone’s attention.
Onel de Guzman was trying to steal Internet access. He ended up composing the “Love Bug”, a computer worm written in VBS that had two main functions. It arrived as an attachment in an email with the subject line of “ILOVEYOU”. When someone opened the file, the worm stole the person’s passwords. Then it used their email account to send copies of itself to everyone in their contacts list. The result was an estimated loss of more than six billion dollars. Guzman wasn’t punished because computer crimes weren’t specifically against the law in most places at the time.
Many of the companies that got hit with the Love Bug invested in backup technology. Backup and recovery software packages like Commvault, Backup Exec, and Acronis started to earn their place in permanent IT budgets and staffing. The Love Bug was big, and it caused some level of industry change. Especially in larger corporations. Smaller shops still struggled to justify a capital investment for “something that just sits there doing nothing most of the time”. As it turns out, the universe was not done teaching us its lesson.
I don’t remember the exact date, but somewhere around the Christmas season of 2010 one of my colleagues asked me to come take a look at something on his screen. There was a full screen dialog box on his monitor that couldn’t be dismissed or minimized. It informed us that his files had been encrypted using a private key. Furthermore, it stated the only way to get access to the files back was to contact a sketchy international phone number and pay them a ransom. It was my first run-in with commercial ransomware.
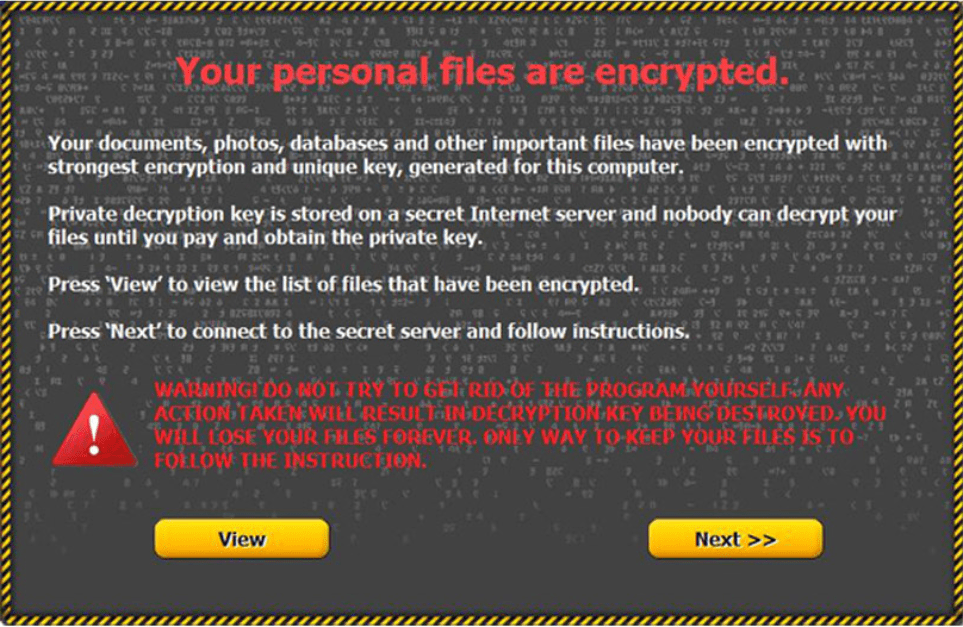
The impact to businesses from ransomware has been enormous. In my opinion, nothing has transformed backup and recovery strategies across the industry more than ransomware’s direct financial impact. All of the sudden, your companies’ data and systems didn’t have to be valuable to a third party to make you a target for computer criminals. Small businesses were practically defenseless against these types of attacks, and the black hats of the world knew it. Organized dark business that operated on Bitcoin sprang up to blackmail the world’s companies into paying to get their own data back. They made away with untold billions in pure un-taxed and un-traceable profit.
One of the best defenses against ransomware was and is a good backup and recovery strategy. Companies rushed to move their data into the cloud where it was copied multiple times. Other organizations hired MSPs to get the technical help they needed to implement sound backup strategy. The “No thanks, I’ll just have my IT team restore it” answer, really took the wind from the bad guy’s sails. Making restoring faster and easier than paying has had the effect of robbing the entire dark business model of its profit motivator.
Ransomware still exists, but it has been diminished. Start-ups rarely enter the market without proven backup and restoration methods now. Investors know to inquire about recovery options. Work forces have been trained to scrutinize the minute details of emails and other incoming communications. Security scanners and teams have been deployed. Data loss is taken seriously by business leaders that used to be far removed from IT.
If my time in IT has taught me anything, it’s that the “next big thing” is just around the corner. Whether that thing is a marvelous invention, or the next super effective way of robbing the world’s companies is always a gamble. Now that most of us have backup solutions in place, the challenge is to not become complacent. Automation fails; backups can be located and compromised, and restoring isn’t an answer to the problem if it takes too long. When was the last time you fully tested restoring your company’s data? Today is a good day to get started on that.