Several of the solutions for controlling mobile data on the market claim to have provide simple solutions, but only one of them has impressed me. Microsoft’s Intune Endpoint Device Manager is extremely robust and very complicated. However, if you forget about trying to push apps and manage user profiles for now and concentrate on securing your corporate data on mobile devices, you’ll find Intune has a trick the others don’t.
Microsoft’s leg up comes from the fact that the software that is most likely being used to access company data is theirs, or one of their partners. Embedded in smart device apps like Outlook, Office, OneNote, Teams, Adobe, Box, Zoom and other popular titles is a process that checks for a special DNS record every few hours. If the record is found, its presence informs the device that there may be an Intune Mobile Application Policy configured for it’s user. The full list of apps that contain this feature is available on Microsoft’s site Supported Microsoft Intune apps | Microsoft Docs.
If you configure a Mobile Application Management policy and assign that policy to a user, when that person uses their company credentials with the specified program, they will be prompted to complete the protection process you have specified. You will also be able to stop access to the clipboard, prevent interactions of corporate data with non-approved apps, require extra device security, and more. Depending on the options you set in the policy, they will loose access to the resource if they refuse. No emailing codes to users, no trying to get them to follow odd instructions on a web page from their phone, they just open the app they have always used and follow the instructions.
Your accounts need to be licensed to use Intune before you can get started. The licenses are included with the Business Premium edition of Microsoft 365, they’re also included with several versions of Enterprise licensing. Licenses for Intune can also be purchased individually. Check Microsoft’s page for more details Licenses available for Microsoft Intune | Microsoft Docs.
Once you have the licenses taken care of you’ll need to configure your tenant. Assuming that you already have Microsoft 365 setup with your custom domain and user accounts, you’ll need to create a couple of DNS records for Intune. Log on to your public DNS host and create a CNAME for EnterpriseEnrollment.company_domain.com that points at EnterpriseEnrollment-s.manage.microsoft.com. Create another CNAME record for EnterpriseRegistration.company_domain.com that points at EnterpriseRegistration.windows.net. More detailed information about the full setup is available at Set up Microsoft Intune | Microsoft Docs and at Set up enrollment for Windows devices by using Microsoft Intune | Microsoft Docs.
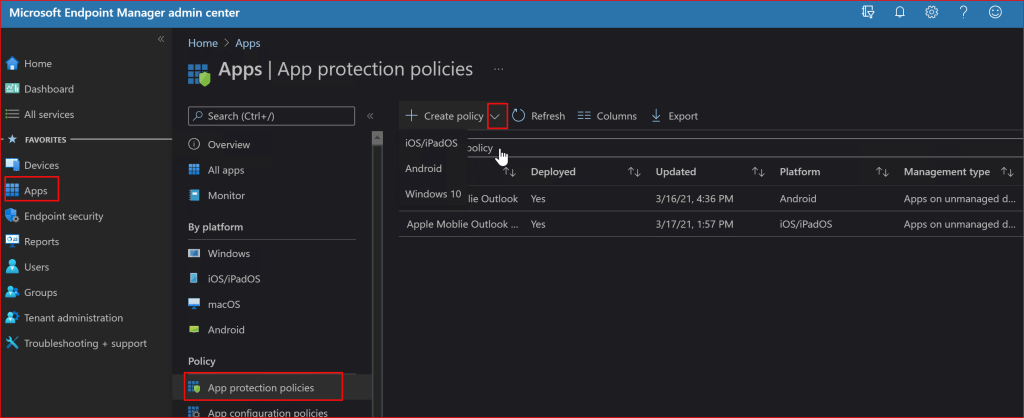
Once the basic setup is finished it is time to setup your first mobile application policy. In this post we’ll create a rule for Outlook. Log on to your Microsoft 365 admin portal and go to Admin -> Show All -> Endpoint Manager -> Apps -> App Protection Policies. Then click the drop down next to the Create Policy button and choose the OS you want to make a policy for.
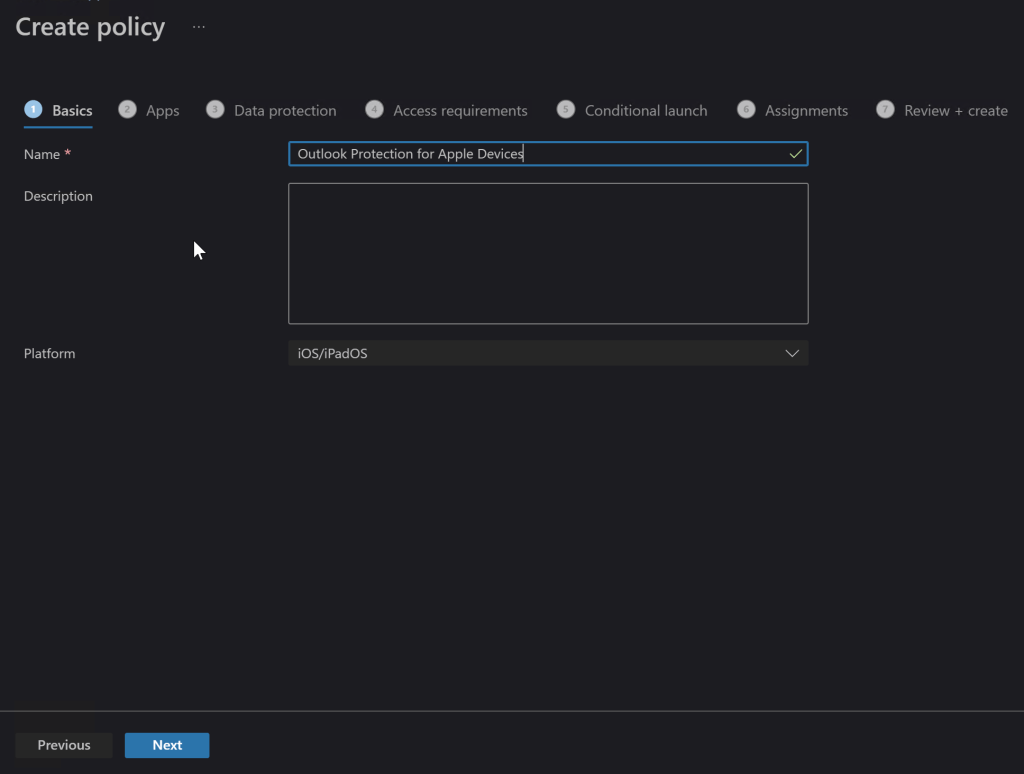
On the next screen, name your new policy something appropriate and add a description if you like. Click Next.
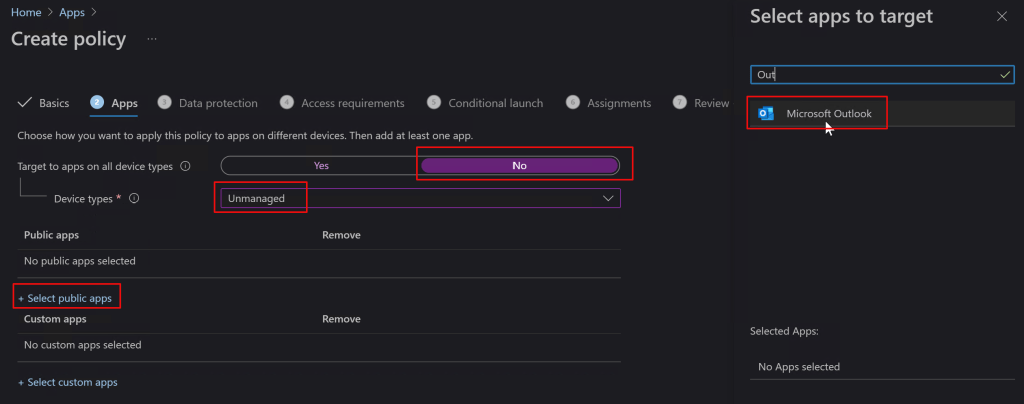
On the Apps screen, toggle the option to Target All Device Types to “No”. Then use the drop down to select device types and check “Unmanaged”. Now click the link to select public apps and type the name of the application you are interested in protecting in the search box, in our case Outlook. Select it and then click the next button to continue.
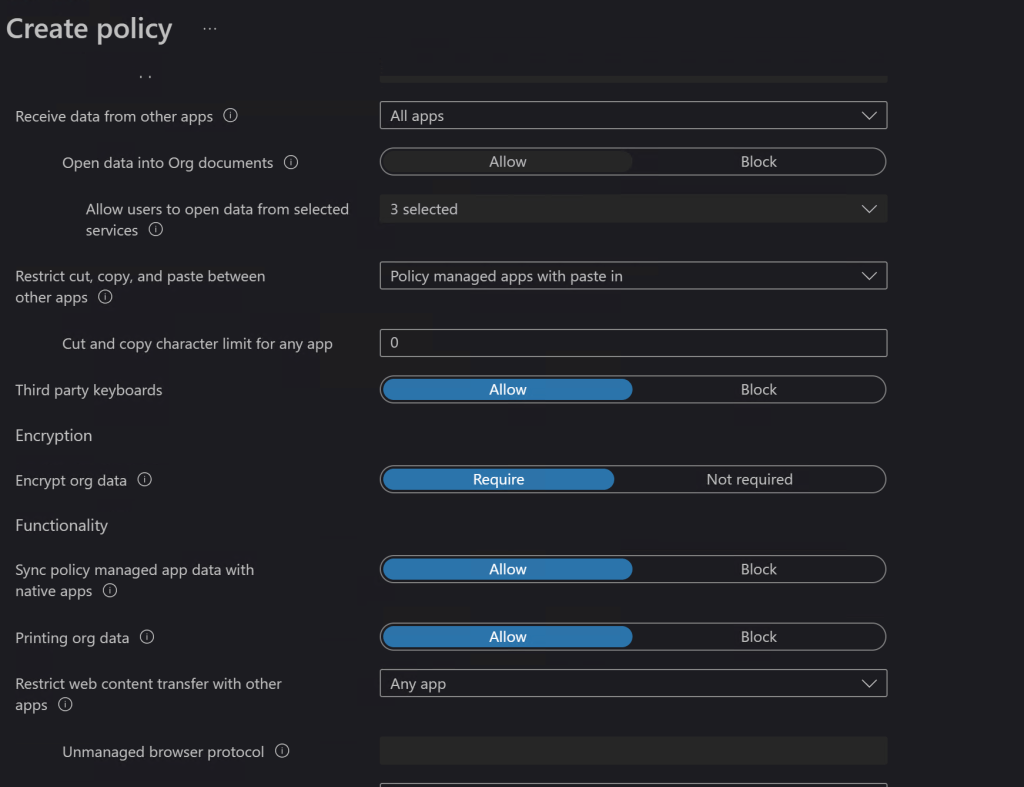
On the Data Protection screen you’ll choose the options that you feel best protect your corporate resources. Will you let them print from Outlook? Should the app encrypt the data on phone or tablet? What about copying and pasting between apps? There are lots of choices and combinations to choose from. Luckily the explanations are pretty straight forward. If you need more information the official Microsoft documentation is located here for iOS: iOS/iPadOS app protection policy settings – Microsoft Intune | Microsoft Docs and here for Android: iOS/iPadOS app protection policy settings – Microsoft Intune | Microsoft Docs.
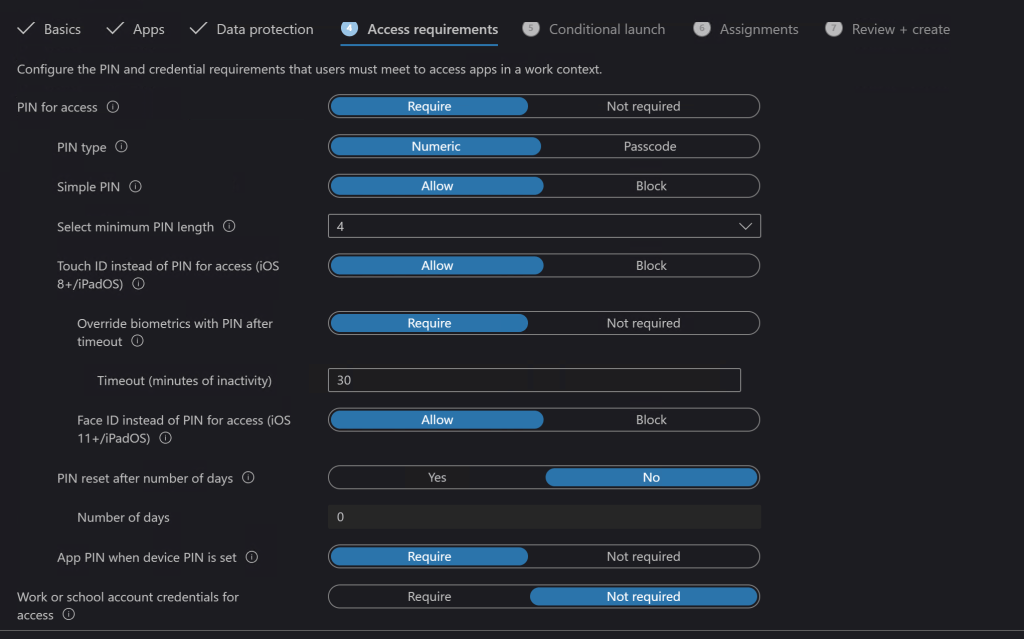
Next up are the access requirements where you will choose what hoops the devices have to jump through to access your data (Outlook). Do they need a device PIN? Should Outlook have its own PIN that prompts every time they open it? Are you going to allow the devices biometric features? There are a lot of choices in this section. I can tell you from experience that these choices are what will annoy your co-workers the most, so don’t be more aggressive than you need to.
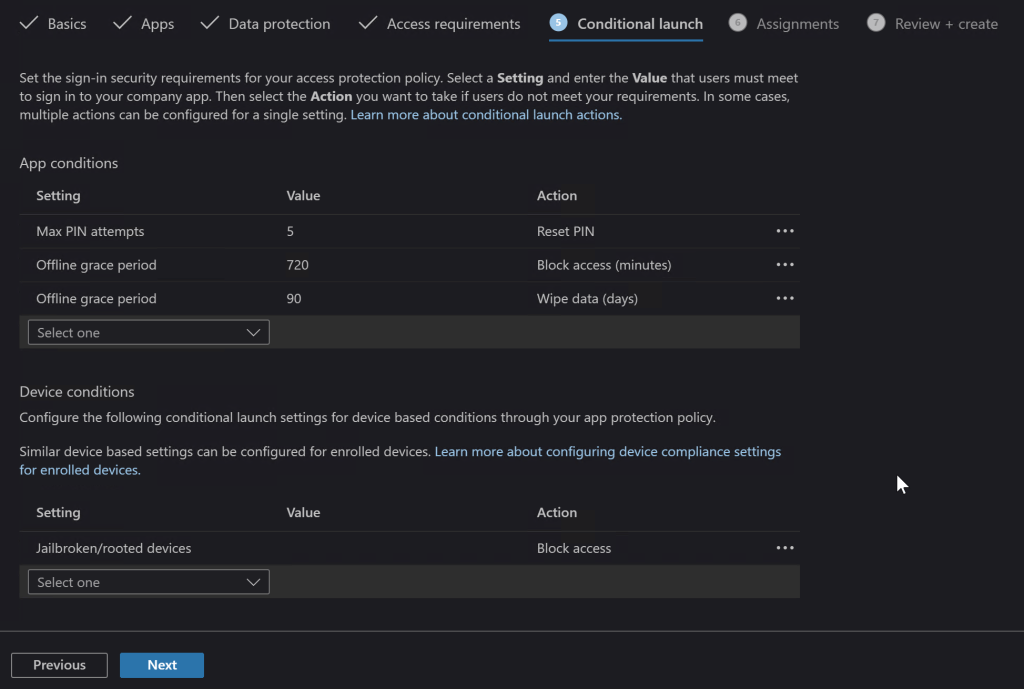
Launch conditions let you control certain aspects that are required for your user’s device to open the app (Outlook) in the first place. A popular choice is to block jailbroken or rooted devices since they are more likely to contain malware. You may also want to consider warning users when their devices are on old versions of their operating systems.
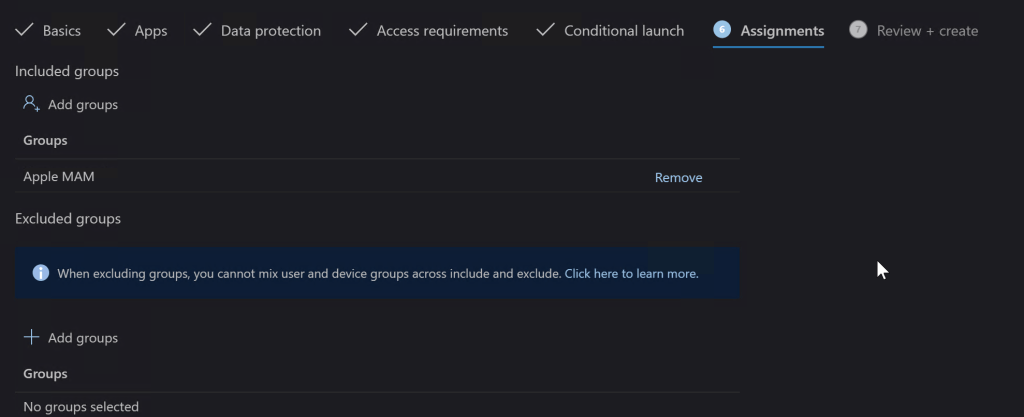
The Assignments tab is where you select the groups of users that the rule you made either applies to, or those that are excluded from it. I typically use the inclusive option and create a group that matches the rule name. If you don’t already have a group that will work you do not need to exit the Endpoint Manager session to make one, you’ll loose your progress and have to start over if you do. Just open another tab in your browser and go to Microsoft 365 admin center – Groups to create your group and add the users. Then switch back to the Endpoint Manager tab and add the group you’ve created.
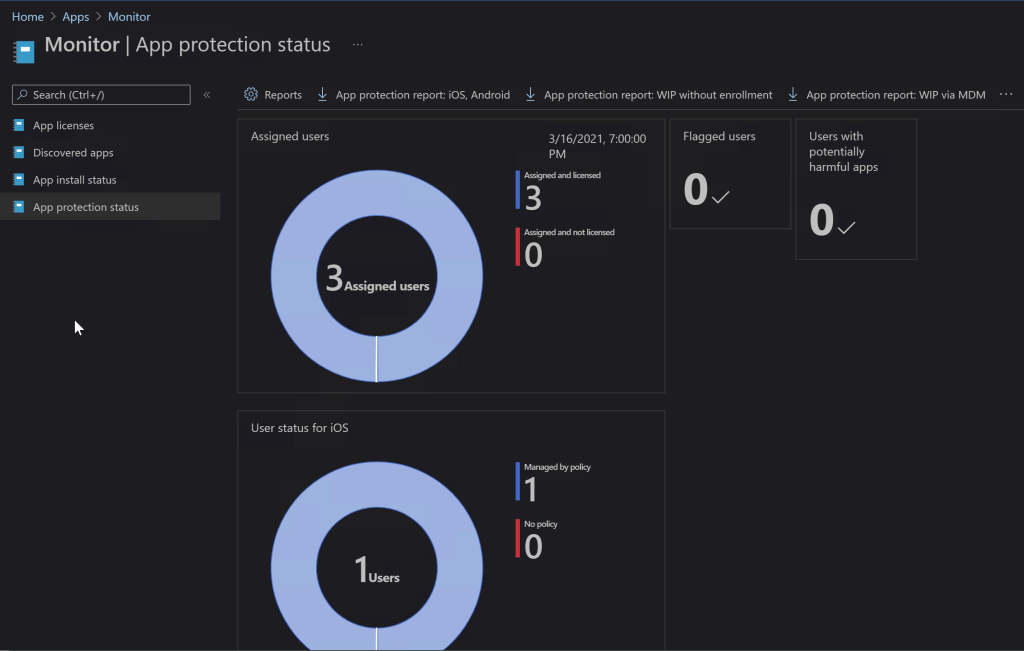
On the last screen you be given a chance to review all the options you’ve selected and create the rule. It can take up to eight hours before Microsoft deploys the rule in your instance of Intune and up to eight more before the devices check in and get the policy applied, be patient. You can check on the status of your rules and devices by using the monitor. In the Endpoint Manager console go to Home -> Apps -> Monitor -> App Protection Status to see the available options.
In today’s world every business should take steps to protect their data. Until the age of ransomware, small businesses were largely exempt from the perils of hackers. Now they are prime targets, data doesn’t need to be valuable on the black market. It only needs to be worth something to you and your company. Often when we think about security we focus on computers and servers, but our mobile devices have just as much access and we don’t want to leave them vulnerable. If all of this proves a bit much to tackle on your own, don’t let that stop you. Reach out to a Microsoft 365 partner or Microsoft themselves and get your mobile endpoints protected.
